Backed by Y Combinator From the #1 US hacking team
Backed by Y Combinator From the #1 US hacking team Leave nothing to chance.
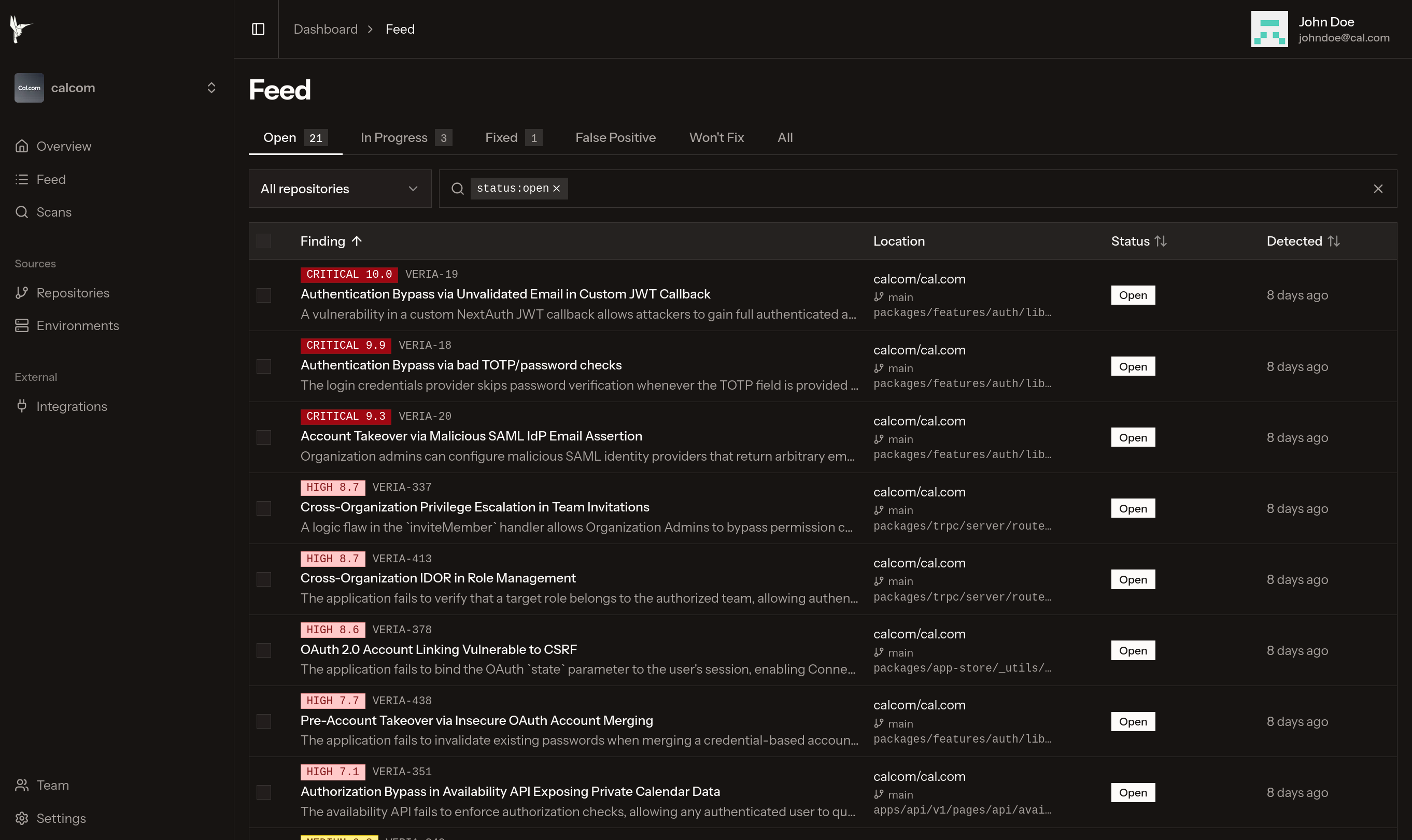
Veria autonomously maps, exploits, and secures your entire attack surface.
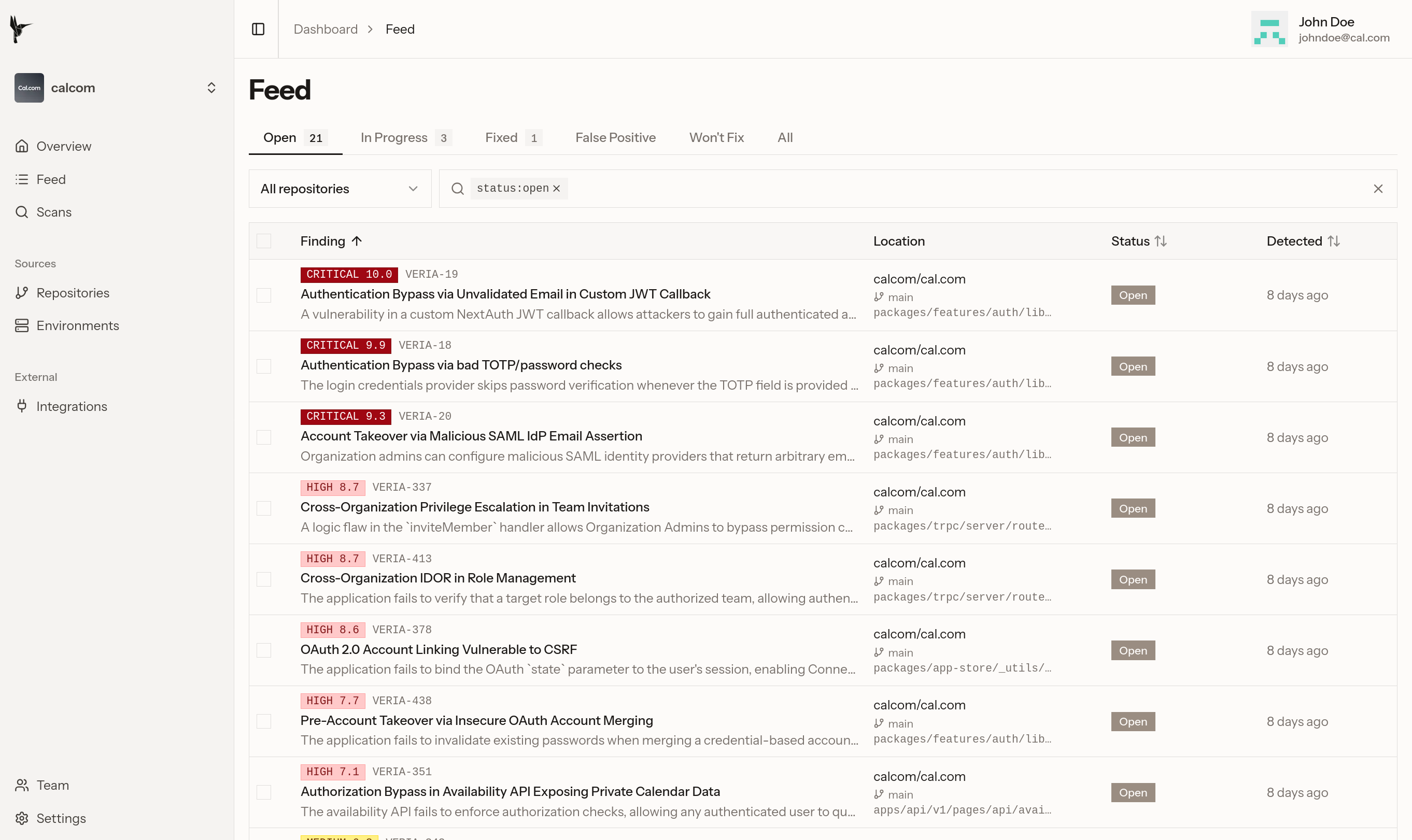
Here's how it works
Connect
Define scope by adding Git repositories and cloud environments, and you're good to go.
Find
We deeply analyze your application for vulnerabilities, from code paths to cloud.
Authentication Bypass Detected
REASONING
I'm currently analyzing this function. It seems
which lets an attacker submit a totpCode
bypassing password authentication
suggest that this function should ensure the user
Exploit
We generate a PoC ran directly against your staging environment, so you can be sure you’re receiving real vulnerabilities.
Secure
For each vulnerability found, we provide an actionable report and suggested patches, so you can quickly secure your application.
Authentication Bypass via bad TOTP + password checks #9
Fixes Authentication Bypass vulnerability in next-auth-options.ts
Blog
Our team shares cutting-edge research, vulnerability discoveries, deep dives into the latest security threats, and the occasional company update.
Case Studies
See how we help teams find and fix critical vulnerabilities before they reach production.
Cayden L.
Founder

Stephen X.
Founder
Jayden S.
Founder
A Letter from the Founders
We're hackers. We run the #1 competitive hacking team in the United States. We've spent years doing offensive security at the highest level. We've been quietly finding and reporting critical bugs, preventing hacks that could've ranked among the largest in history.
Over time, we kept seeing the same thing: companies getting hacked by vulnerabilities we'd spot in minutes. Not because their teams are incompetent; they're doing everything by the book.
Pentests are expensive and rare. SAST tools don’t understand your program. Security feels like a tax on shipping. Teams have to choose between speed and safety. Speed wins, and vulnerabilities slip through.
But it doesn't have to be this way. We know what security can look like, and it matches the speed and scale of development.
Let's build the future of security together.